FBI Director Kash Patel issued a stark warning on Friday, revealing that Russian intelligence services are conducting a sophisticated phishing campaign aimed at Americans deemed to possess "high intelligence value." The operation specifically targets users of private, encrypted messaging applications, with the Signal platform identified as a primary vector.
Targets and Tactics
According to Patel, the campaign's victims include current and former U.S. government officials, military personnel, elected politicians, and members of the press. The joint advisory from the FBI and the Cybersecurity and Infrastructure Security Agency (CISA) details that Russian operatives are sending deceptive messages that appear to originate from platform support teams. These messages contain links or requests for login credentials that, if acted upon, grant the hackers full control of the victim's account.
"Globally, this effort has resulted in unauthorized access to thousands of individual accounts," Patel stated in a social media post. "After gaining access, the actors can view messages and contact lists, send messages as the victim, and conduct additional phishing from a trusted identity." He emphasized that the vulnerability lies not with the applications themselves, which use end-to-end encryption, but with user behavior. "It's important for you to be aware and take action—this vulnerability is not with the application—but you as the end user," he continued.
Broader Implications and Official Response
The agencies warned that while Signal is a current focal point, these phishing methods could be adapted for use against other similar encrypted messaging services. The compromised accounts provide a powerful intelligence-gathering tool and a platform for further disinformation campaigns. "If the user performs any of the requested actions, they unwittingly provide the actors with unauthorized access to their account either by adding the attacker's device as a linked device or through a full account takeover," the joint report explained. It further cautioned that the campaign could evolve to include malware deployment.
In response, the FBI and CISA have urged at-risk individuals to exercise extreme caution with unsolicited messages, avoid clicking on suspicious links, and immediately report any suspected phishing attempts. The disclosure underscores the persistent and evolving cyber threat posed by state actors, even on platforms designed for secure communication.
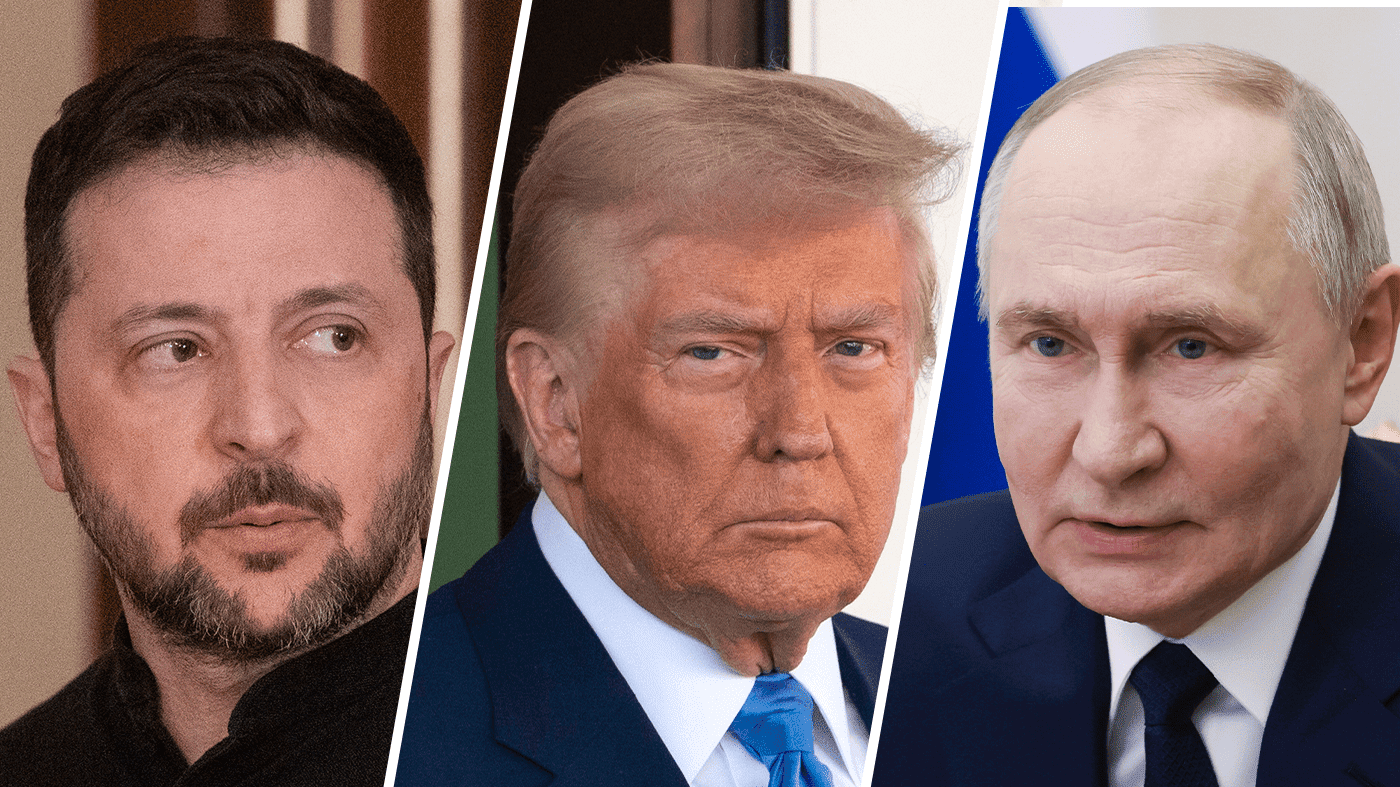
This incident also casts renewed light on the government's own use of private messaging apps for official business. A recent, highly critical inspector general report found that Defense Secretary Pete Hegseth violated department policy and potentially jeopardized operational security by using Signal on a personal device. This practice came to public attention last year when an Atlantic journalist was accidentally added to a high-level Signal group chat discussing potential strikes on Houthi rebels, revealing the Trump administration's reliance on the platform for sensitive conversations. The ongoing conflict in the Middle East continues to test U.S. diplomatic and military posture, as seen when the previous administration paused planned strikes on Iran, claiming a diplomatic opening.
The Russian campaign arrives amid heightened global tensions and increased scrutiny of digital security for public figures. The targeting of journalists is particularly notable, as a free press is a cornerstone of democratic society. Recent moves by other government agencies have also drawn attention to the relationship between officials and the media, such as when the Pentagon closed a press workspace and escorted journalists out following a legal challenge to its media policy.
This sophisticated phishing operation represents a direct challenge to national security and the integrity of private communications among America's leadership class. It serves as a potent reminder that technological tools for privacy can be undermined by human error, and that geopolitical adversaries are continuously refining their methods to exploit such weaknesses.